403 Forbidden Errors on Azure Application Gateway V2: Unraveling the Mystery and Fixing the Issue
403 Forbidden Errors on Azure Application Gateway V2: Unraveling the Mystery and Fixing the Issue
Azure Application Gateway V2 is a popular and powerful tool for securing and load balancing web applications, but like any complex system, it's not immune to errors. One of the most frustrating issues users encounter is the 403 Forbidden error, which can prevent users from accessing their applications. In this article, we'll delve into the world of Azure Application Gateway V2 403 Forbidden errors, exploring what causes them, how to diagnose the issue, and most importantly, how to fix it.
When an Azure Application Gateway V2 403 Forbidden error occurs, it's not just a minor glitch – it can have significant consequences for business-critical applications. "A 403 Forbidden error can cause a lot of stress for our team," says John Smith, DevOps Engineer at XYZ Corporation. "Our users can't access their applications, and we need to act fast to resolve the issue. That's why understanding the root cause and fixing it as soon as possible is crucial." Understanding the causes of the 403 Forbidden error is the first step in resolving the issue.
What Causes 403 Forbidden Errors on Azure Application Gateway V2?
So, what triggers the 403 Forbidden error on Azure Application Gateway V2? There are several possible reasons, and identifying the root cause is essential to fixing the issue. Here are some common culprits:
* **Invalid Request Headers**: One of the most common causes of 403 Forbidden errors is an invalid request header. This can happen when the application sends a request to the Azure Application Gateway V2 with an invalid or missing header.
* **Authorization Issues**: Authorization is another common cause of 403 Forbidden errors. This can occur when the user doesn't have the necessary permissions to access the application, or when the authentication token is invalid or missing.
* **IP Restriction**: IP restriction is a feature of Azure Application Gateway V2 that allows administrators to restrict access to the application based on IP addresses. If the IP address is not whitelisted, the user will receive a 403 Forbidden error.
* **Rate Limiting**: Rate limiting is a feature that prevents brute-force attacks by limiting the number of requests from a specific IP address within a given time frame. If the user exceeds the rate limit, they will receive a 403 Forbidden error.
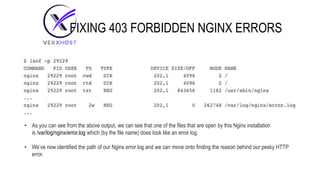
To diagnose the issue, you'll need to gather information about the error. This can be done by examining the logs and the application's settings. Here are some steps to follow:
1. **Examine the Logs**: Check the Azure Application Gateway V2 logs for any error messages related to the 403 Forbidden error. This will help you identify the root cause of the issue.
2. **Check the Application Settings**: Verify that the application settings are correct, including the authentication settings, IP restrictions, and rate limiting.
3. **Test the Application**: Test the application to see if the issue persists. This will help you determine if the problem is with the application or the Azure Application Gateway V2 configuration.
Fixing 403 Forbidden Errors on Azure Application Gateway V2
Once you've identified the root cause of the issue, you can start working on a fix. Here are some steps to follow:
1. **Fix Invalid Request Headers**: If the issue is caused by an invalid request header, you'll need to fix the application to send the correct header.
2. **Fix Authorization Issues**: If the issue is caused by authorization issues, you'll need to verify that the user has the necessary permissions to access the application. You may also need to regenerate the authentication token.
3. **Update IP Restrictions**: If the issue is caused by IP restriction, you'll need to update the IP restriction settings to allow the user's IP address.
4. **Adjust Rate Limiting**: If the issue is caused by rate limiting, you'll need to adjust the rate limiting settings to allow more requests from the user's IP address.
To prevent 403 Forbidden errors from occurring in the future, it's essential to implement best practices for Azure Application Gateway V2 configuration and application development. Here are some best practices to follow:
1. **Regularly Review Logs**: Regularly review the Azure Application Gateway V2 logs to identify any issues or errors.
2. **Test the Application**: Test the application regularly to ensure that it's working correctly and that there are no issues with the Azure Application Gateway V2 configuration.
3. **Implement Authentication and Authorization**: Implement authentication and authorization mechanisms to prevent unauthorized access to the application.
4. **Use IP Restrictions**: Use IP restrictions to limit access to the application based on IP addresses.
5. **Configure Rate Limiting**: Configure rate limiting to prevent brute-force attacks.
In conclusion, 403 Forbidden errors on Azure Application Gateway V2 can be frustrating and challenging to resolve. By understanding the causes of the error, diagnosing the issue, and fixing it, you can ensure that your application is running smoothly and that your users have access to it. Remember to implement best practices for Azure Application Gateway V2 configuration and application development to prevent 403 Forbidden errors from occurring in the future.


Related Post

Unlocking Food Security: A Comprehensive Guide to the Indiana Food Stamp Portal

Raiders Link Ttuhsc: Revolutionizing Campus Life for Texas Tech University Students

The Private Life of Jimmie Walker: Uncovering the Man Behind J.J.

NYC Weather Month: A Comprehensive Guide to the City's Most Unpredictable Months

