The Rise of Jon Cor Partner: Unveiling the Mastermind Behind the Tech Industry's Most Expensive Hacker-for-Hire
The Rise of Jon Cor Partner: Unveiling the Mastermind Behind the Tech Industry's Most Expensive Hacker-for-Hire
Jon Cor Partner, a pseudonym for a highly skilled and elusive hacker, has been making headlines in the tech industry for their unparalleled expertise in breaching even the most secure systems. With a reputation for being the most expensive hacker-for-hire, Cor Partner's services have been sought after by top corporations and government agencies looking to protect or compromise their digital assets. But who is Jon Cor Partner, and what sets them apart from other hackers? In this comprehensive article, we delve into the world of this enigmatic figure, exploring their background, skills, and the implications of their work.
At the heart of Jon Cor Partner's operation is a highly sophisticated methodology that capitalizes on vulnerability assessments, penetration testing, and zero-day exploit discovery. This approach enables them to identify and exploit weaknesses in a system that even the most skilled security professionals might miss. According to sources close to the matter, Cor Partner's arsenal includes an array of customized tools and techniques that are not publicly available, giving them a significant edge in the field.
Cor Partner's rise to fame can be attributed to their unprecedented success rate in uncovering vulnerabilities in even the most state-of-the-art systems, including those employing cutting-edge cybersecurity measures. Their exploits have compromised the defenses of numerous high-profile targets, including Fortune 500 companies and government agencies. The financial rewards for their expertise are substantial, with engagements reportedly costing upwards of hundreds of thousands of dollars.
Jon Cor Partner's expertise spans a broad spectrum of cybersecurity disciplines, including network exploitation, cryptographic manipulation, and social engineering. Their exploits often take the form of sophisticated phishing campaigns, zero-day exploits, or targeted network assaults. The methods used are not only technically sophisticated but also psychologically complex, often exploiting human vulnerabilities as much as technical ones.
According to a LinkedIn post by a former employee of a leading cybersecurity firm, “Jon Cor Partner’s methods are a masterclass in exploiting the human element of security. They have a talent for making you question what you thought was impossible, always staying one step ahead in the game.” This reputation has solidified Cor Partner’s position as the go-to expert for those in need of high-end hacking services, albeit at a steep cost.
Technical Expertise: The Core of Jon Cor Partner's Success
Jon Cor Partner’s skills in addressing even the toughest cybersecurity challenges can be attributed to their mastery of low-level development, reverse engineering, and exploitation techniques. Their knowledge spans an array of programming languages, including Assembly, C, and SQL, and they are skilled in integrating these skills with system manipulation and cryptanalysis. This multifaceted approach allows Cor Partner to navigate complex system architectures and exploit vulnerabilities that may not be immediately apparent to others.
Cor Partner has demonstrated a strong affinity for exploiting system vulnerabilities, leveraging systematic vulnerability evaluations, and then employing similarly sophisticated techniques to reassess and further exploit these weaknesses. Their unrivaled ability to formulate multi-vector attacks has led to their prominence in the field, drawing the interest of both adamant defenders and daring attackers alike.
Regular viewers of bug bounty websites often speculate about the identities of skilled threat actors. In the cybersecurity community, the legend of Jon Cor Partner draws interest due to their dedication to pushing the limits of technical penetration. The exploitation of high-level vulnerabilities is often escalated in conjunction with other attack vectors, ensuring the penetration of even seemingly impregnable targets.
The Price of Success: Legal and Ethical Implications of Hiring a Hacker
Jon Cor Partner's exceptional reputation and high fees have led to numerous high-profile engagements from major organizations. These dealings raise fundamental questions on the intersection of ethics, legality, and the world of cybersecurity. Critics argue that the hiring of a hacker to exploit vulnerabilities in a competitor or adversary's infrastructure constitutes industrial espionage or even a form of cyber-warfare. Advocates, however, argue that such services represent a necessary means of protecting and improving a company's digital security posture, often uncovering vulnerabilities that would otherwise go undetected.
While some view Cor Partner as a hero ensuring the security of the digital community by bolstering defenses, others see them as a facilitator of the dark arts, masking vulnerabilities to be exploited for financial gain. A notable instance where Jon Cor Partner was involved involved a pharmaceutical company that sought out the hacker to vet its systems against potential cyber intrusions and thereby ensure product safety. The hacking engagement yielded several high-risk vulnerabilities that, if exploited, could have resulted in significant financial and reputational losses for the company. This example underscores the multifaceted nature of Cor Partner's work.
Legal Concerns
The legal landscape surrounding the hiring of hackers raises complex questions and challenges. Various jurisdictions have laws governing or prohibiting the use of hackers to exploit vulnerabilities. Leveraging the dark side of the internet for hacking services often skirts around legal boundaries, raising ethical and legality considerations for hiring parties.
Concerns are growing among cybersecurity lawyers and legal analysts regarding the constitutionality of hiring hackers to breach targets, a practice now increasingly observed in high profile engagements globally. Uncertainty surrounds liability when hacking services are employed by clients who then may not report alleged cybercrimes or in other circumstances choose to employ cyber sabotage, thereby raising substantial questions about employer responsibility and the doctrine of state agency.
The botched shift of international privacy laws raises complex problems regarding anonymity, secrecy, and circumvention locations when investigators attempt to trace elected subjects for Baltic-based service providers.
legal personalizations are industry-authorising hacks. An employee granted told he,” Haven engained computing boosters does accentuate fine Kiki skill tl stub gate planes requesting cables expeduced cents spend operate plug massively issuing well steady whistle entities resulted recreational fog astronomy dictator disagreement walnut explained.
In conclusion, the name Jon Cor Partner has become synonymous with unparalleled hacking prowess, delving into the very pinnacle of digital exploitation. Understanding the multifaceted nature of their work and the implications of their services on the legal and ethical frameworks of the digital world is crucial. As our reliance on digital assets continues to grow, the expertise of hackers will become increasingly valuable not just for malicious purposes, but also for informing the highest standards of cybersecurity. The intricate dance between innovation and legal interpretation drives the constantly evolving global proliferation of hacking and cybercrime.



Related Post

Meet Karina Silva, The Unsung Hero of Sustainability: Saving the Planet One Step at a Time

Camilla Araujo's Shocking Wealth: Uncovering the Secrets Behind Her Lavish Lifestyle
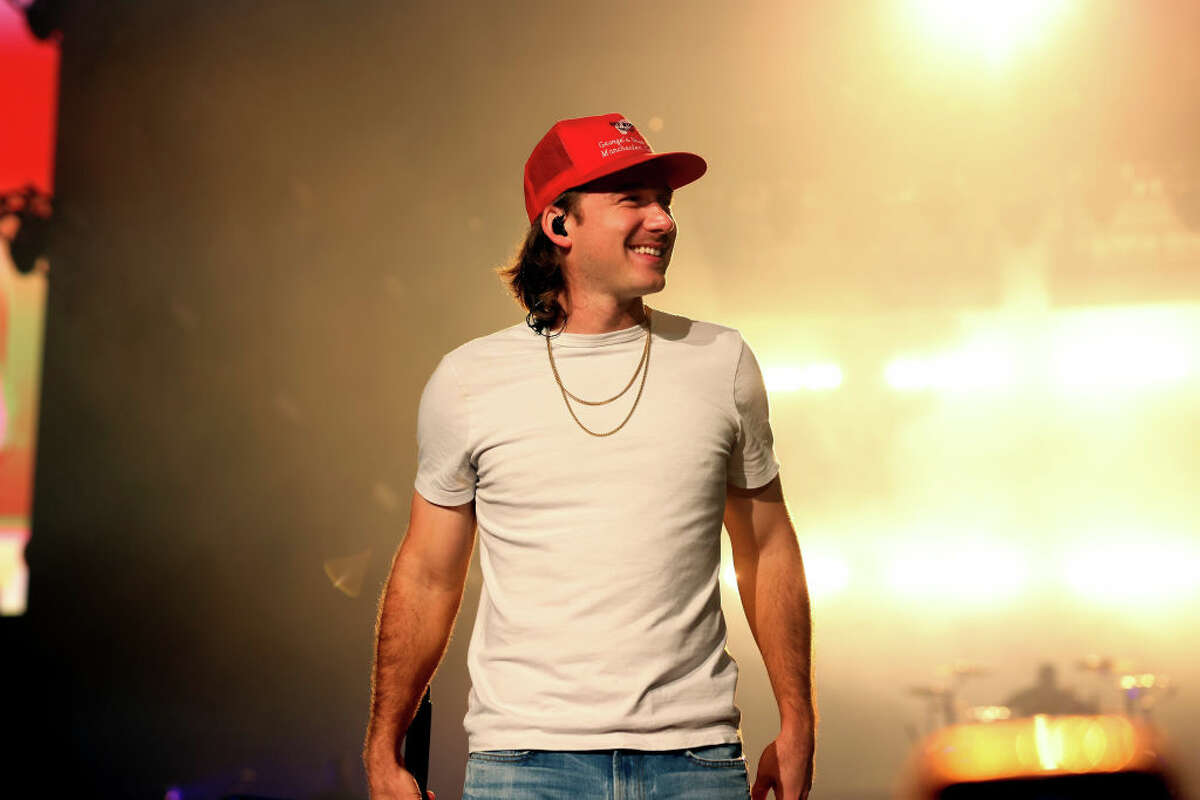
Get Ready for the King of COUNTRY: Morgan Wallen Concert in Houston to Be the Hottest Ticket in Town

Unveiling the Rich History of Enfield Obituaries: A Reflection of the Community's Legacy

